Dear White-Hats,
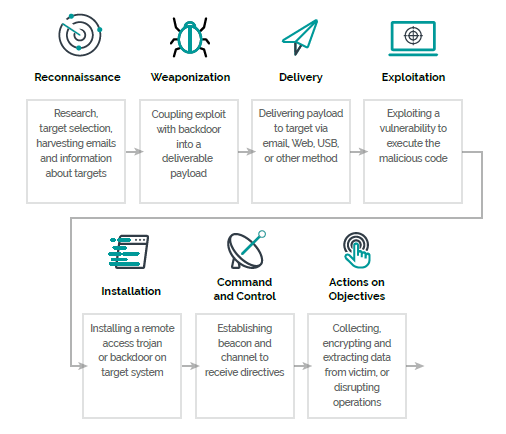
what an amazing experience we had with Kali Linux. Thanks to everyone who participated, we now have a overview of how cyber attacks work. We got to know Kali Linux as the main tool for Hackers. Our Speakers gave you a guided tour of a cyber attack along the Cyber Security Kill Chain. Thank you so much!
Before it goes into the well-deserved time-out, here’s again our small call for action: Take our spirit into the world and tell your friends and colleagues about it. Maybe you even feel like acting as a speaker or know someone who wants to introduce us to his topics. Are there any topics that matter to you? Let us have your wishes.
See you next time and all the best!


Sende eine Antwort zu „Trust in Tech – September Kali Workshop“