Trust in Tech – Modern Awareness Building through Nudging, Gamification & Co – Quick Recap
Modern Awareness Building through Nudging, Gamification & Co: Why is Psychology So Important in Cyber Security? How do employees become the human firewall of a company? Dr. Niklas Hellemann from Cologne-based SoSafe GmbH presented current findings from cognitive psychology and learning theory and their implications for modern security awareness programs – mixed with lively anecdotes and application tips from practice as well as data stories from their own phishing simulation projects for various types of companies. So let us recap some of his findings.
Dr. Niklas Hellemann is a certified psychologist, long-term management consultant and CEO of SoSafe Cyber Security Awareness. As an expert in social engineering, he deals with innovative methods of employee awareness. SoSafe is a young Start-Up, founded in Cologne. Together with Lukas Schaefer and Felix Schuerholz the Team consist of 20+ people from different domains such as CyberSec, Sofware Dev, Design, Marketing and Engineering.
No rise of user focused threats
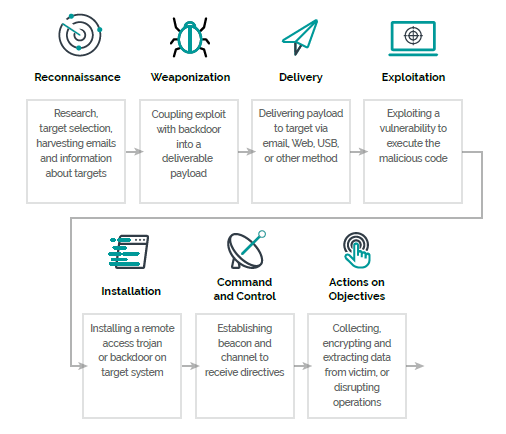
Cybercriminality became a business, phishing quickly took the throne of the most common threats. Small costs but potentially high revenue is what Cybercriminals can expect. According to data from Proofpoint and Forbes 91 Percent of all threats start with a phishing mail, causing damage up to 3 million Euro in 2018. Especially small-mid organizations with an underdeveloped security posture are preferred targets.
Cybercriminals don`t aim for the technical solutions like exploits, as the Service as a Service market grew larger, sophisticated phishing campaigns can be build with less resources. These Mails cannot be recognized from spam filters and will find their way to a user.
Next Generation Security Awareness
Regular Security Awareness campaigns like on-site lectures are time consuming, not flexible and hard to apply to all employees. Communication-campaigns via mail are doomed to stay unread and won´t last in the minds.
Next generation security awareness focuses not only on creating awareness but on changing the habits. SoSafe has identified 3 Ways to change habits. Incidential Learning, Nudging and Gamification.
The first is learning through immediate Feedback, Nudges are small “hints” in your daily life that could make you, change your decision (like having fruits in eye sight, when you enter your kitchen). Through gamification will start seeing awareness as a contest, maybe through placing QR Badges at stair-houses.
Some interesting Observations
In one of their interactions, the customers employees probability to click on a mail, has doubled when the supervisor is the sender.
“Loose lips save ships!” – People who don´t work remote are less likely to click on a mail. The communication between the desks is key.
Thank you Dr. Niklas Hellemann for your talk and showing us this side of Cyber Security.